Before you trust company contact, check it Before you trust it, check it.
Give customers, suppliers, employees, partners, and connected systems a way to verify who contacted them, what it is about, and whether protected messages still match what was issued. Use TraceProof through API integrations, or deploy admin-approved operator tools for teams protecting outbound email from Gmail and Outlook. Verify company contact before you reply, pay, approve, or act.
Privacy-respecting by design. TraceProof supports public and private traces, protected message verification, API-based integrations, and operator-led email protection without relying on full message transcript storage.
Trace Verified
Every sensitive outbound contact should make 3 things clearCheck 3 things first
Before someone trusts a call, message, workflow request, AI interaction, payment instruction, or system-to-system update, these basics should be clear.Who sent it, what it means, and whether it still matches.
Who is this?Who sent it?
Verify the company, sender, agent, workflow, or system behind the contact.Confirm who issued the contact.
What is this about?
Show declared context so the recipient understands what the contact, request, or workflow update is about.Review the declared purpose before you act.
Has it been altered?
Check whether protected message content still matches what was issued.Check whether the protected message still matches.
If those basics are missing, legitimate contact gets ignored, automation looks risky, and teams move more cautiously.
Two ways to protect outbound contactTwo ways to use TraceProof
TraceProof can be used by connected systems or by approved operators working in everyday communication tools. Organisations can start with protected email workflows, then expand into deeper API and platform integrations when needed.Use APIs for automated systems, or operator tools for protected email.
API and system integrationsAPI integrations
Connect TraceProof to agents, workflows, CRM, support, finance, messaging, and other systems that issue outbound contact automatically.For agents, workflows, CRM, support, and payment systems.
- AI agents and automated workflows
- System-to-system verification
- CRM, support, payment, and messaging integrations
- High-volume or embedded verification flows
Operator-led message protectionOperator email protection
Let approved users protect outbound messages from Gmail or Outlook using organisation-approved profiles, purposes, templates, and sender identities.For approved users protecting Gmail and Outlook messages.
- Customer support and account updates
- Supplier, finance, and payment-related messages
- Sensitive manual outreach
- Teams that need protection before a full system integration
Where independent verification can reduce trust frictionWhere TraceProof helps
TraceProof is useful anywhere a person or system is asked to trust sensitive contact before acting.Start with sensitive contact people need to trust before they act.
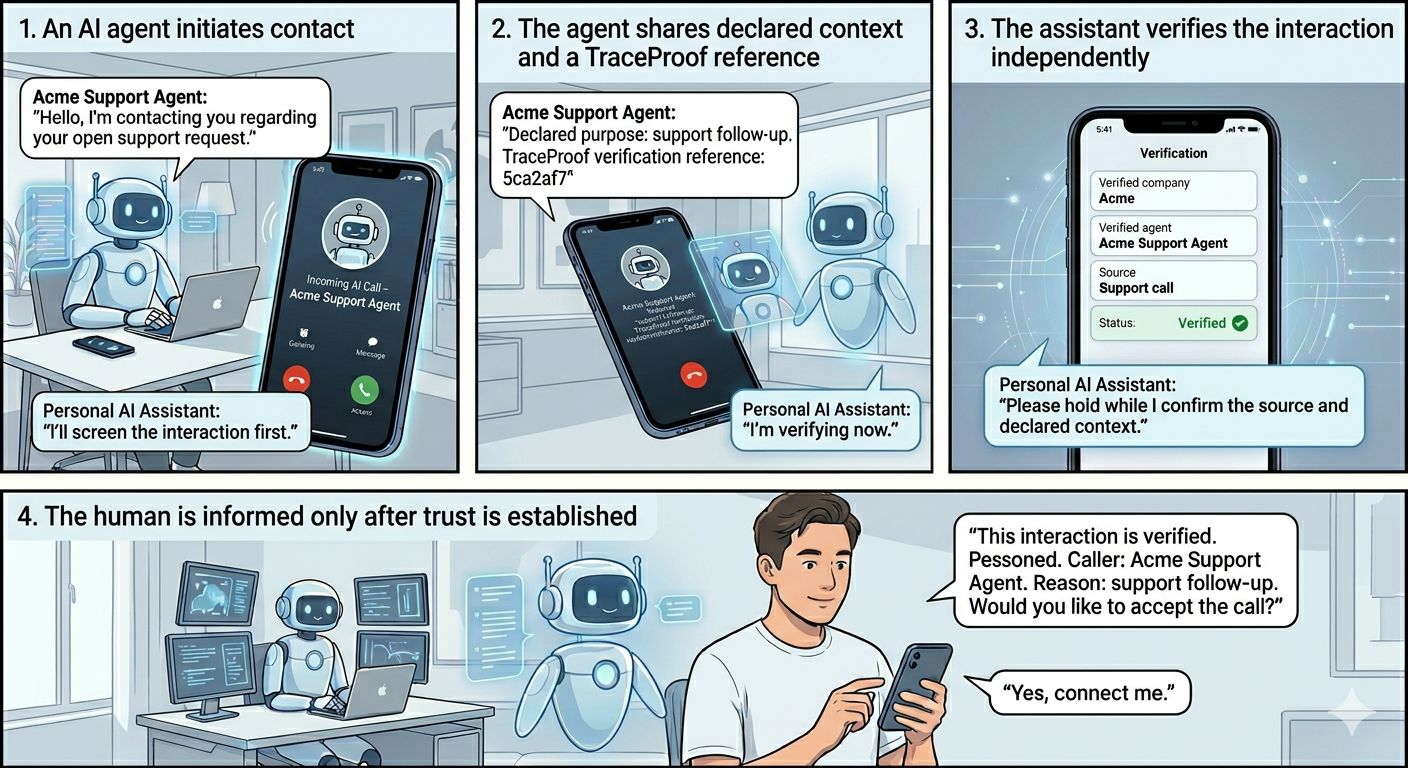
AI outbound customer contactAI and workflow contact
Let customers verify company, purpose, and protected message before engaging with AI-led calls, emails, chats, or service updates.Give automated contact an independent check.
Payment, supplier, and AP instructionsPayments and supplier changes
Attach a verifiable reference to supplier changes, invoice requests, bank-detail updates, or urgent payment instructions before money moves.Reduce risk before sensitive actions.
Customer support and account communicationsSupport and account updates
Make refund updates, account access messages, identity checks, case updates, and support follow-ups easier for customers to trust.Help customers confirm real company contact.
Protected email
Allow support, finance, account, and operations teams to protect sensitive Gmail or Outlook messages using approved profiles, templates, and purposes. Recipients get a TraceProof reference they can check independently before trusting or acting on the message.Protected Gmail and Outlook messages.
Trust that travels with outbound contactHow TraceProof works
TraceProof creates a verifiable trace for outbound contact, binds declared context and proof data to it, and lets people or connected systems verify independently before acting.Create a protected trace and let recipients check it.
Register approved sendersRegister approved sources
Companies register the approved senders, operators, agents, workflows, and systems allowed to issue verifiable outbound contact.Companies define who can issue protected contact.
Create the right traceCreate a trace
When outbound contact happens, TraceProof creates a public or private reference and binds declared context, protected message integrity, and proof data to it. This can happen through an API integration or through approved operator tools such as Gmail and Outlook.TraceProof creates a public or private reference for the contact.
Verify independently
Customers, suppliers, partners, employees, and connected systems can verify issuer, context, message protection, and private access when needed without TraceProof storing full message content.Recipients use the reference to check before they trust it.
Trust without surveillance. TraceProof can verify issuer, declared context, and protected message integrity without keeping full conversations. Optional certified-content checks can be used where file or image integrity matters. You can see TraceProof live in our own verified chat on this page.
Built for issuers, recipients, and connected systemsWho TraceProof helps
TraceProof helps the organisation issuing the trace, the person receiving it, and the system that may need to check it before acting.For teams, recipients, and systems that need to check first.
For teams sending outbound contact
Use TraceProof to add verifiable trust to customer-facing and operational contact, including calls, messages, workflow notifications, AI-powered outreach, and system-to-system updates.Add trust to email, calls, workflows, and AI outreach.
Teams can manage approved senders, operators, agents, workflows, credentials, profiles, purposes, templates, and public or private trace settings from one controlled organisation account.Manage approved sources and templates.
Create a Company AccountFor people receiving it
Recipients can check where contact came from, what it is about, and whether it looks trustworthy before they respond, approve, pay, escalate, or act on it.Check contact before you respond or act.
They can review declared context, check protected message status, open private traces with a second code when required, and save verified traces to their own history.Private traces can require a second access code.
Create a User AccountFor systems checking it
Partners, marketplaces, platforms, and other connected systems can verify before they accept, route, automate, or rely on what they received.Check before a workflow continues.
Connected systems can check issuer status, declared context, protected-message integrity, and optional certified-content proofs before a downstream workflow continues.For partner and platform flows.
Simple pricing to get started
Choose a plan based on shared TraceProof certification volume, protected conversation usage, and agent count.Start small, then scale verification as usage grows.
Developer
Testing and early integrations.
- 1,000 certified interactions / month
- ~16 protected conversations / day*
- 3 agents
Growth
Startups and early live use.
- 7,500 certified interactions / month
- ~125 protected conversations / day*
- 10 agents
Professional
Growing teams and multi-agent live use.
- 25,000 certified interactions / month
- ~417 protected conversations / day*
- 25 agents
Enterprise
Broader rollout and tailored for your needs.
- Tailored certifications
- Tailored protected conversations
- Tailored agents
Exact Image checks are included in the same TraceProof certification plans.
Richer uploaded-image checks are available as an add-on (partial image checks, crops, resizing, etc.)
Frequently asked questions
Answers to common questions about verification, privacy, content checks, and rollout.Quick answers before you start.
What is TraceProof?
TraceProof adds a verifiable trust layer to outbound company contact. It helps organisations show where something came from, what it is about, and whether protected content still matches what was issued.
Does TraceProof store message content or image files?
TraceProof can verify message integrity without storing full message content. Exact image certifications are based on file-byte proofs, and richer certified-image checks are available when the organisation also chooses to include the original file with the certification.
Can TraceProof certify images or other content?
Yes. Organisations can certify images and let recipients verify them in two ways: exact same-file checks from the certified proof, or richer uploaded-image checks when the original file was included with the certification.
Who can verify a TraceProof reference?
Customers, partners, employees, or connected systems can verify the trace they receive. In many flows, Company A issues the trace and Company B, the customer, or another system checks it independently. Organisations can also review verification coverage and integrity checks inside their own trace history.
What does TraceProof verify?
TraceProof can verify where the contact or certification came from, the declared context, the source and time of contact, whether protected messages were covered, and whether content exactly matches or is likely related to a certified original depending on the certification path used.
Can teams use TraceProof without a full system integration?
Yes. TraceProof supports operator-led message protection for approved users working in tools such as Gmail and Outlook. Admins configure the allowed senders, profiles, purposes, and templates. Operators can then protect outbound messages and give recipients a TraceProof reference to verify independently. API integrations can be added later for automated or higher-volume workflows.
Can this work for agent-to-agent interactions?
Yes. The same verification model can support software agents checking where incoming interactions came from, what they are about, and whether protected messages were altered.